Buffer overflow - Wikipedia

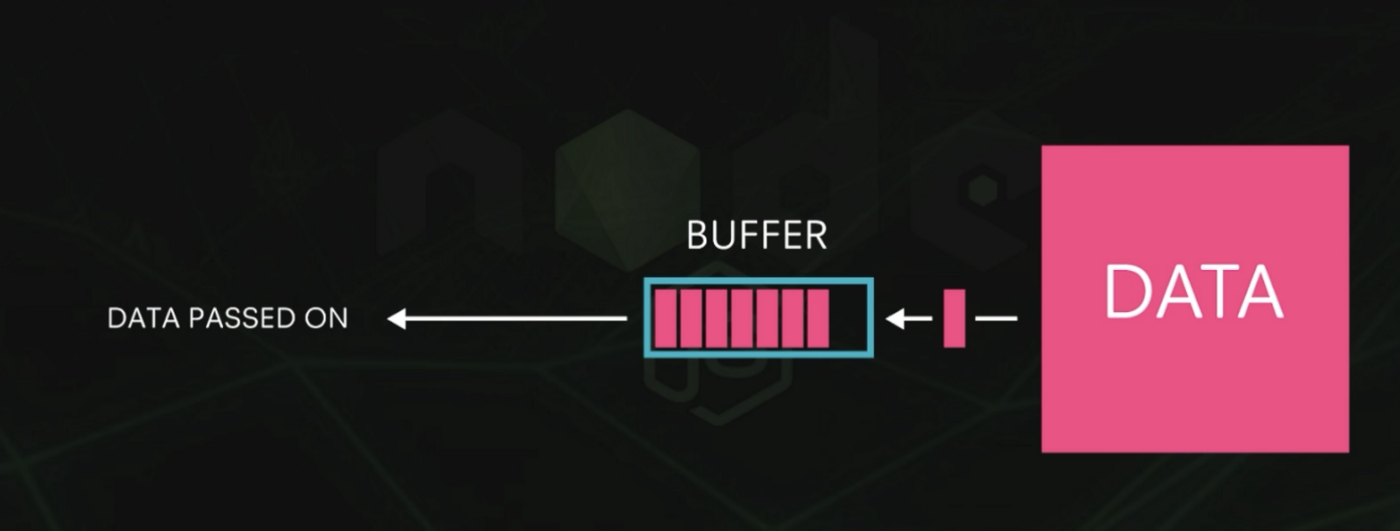
What is a Buffer Overflow Attack – and How to Stop it
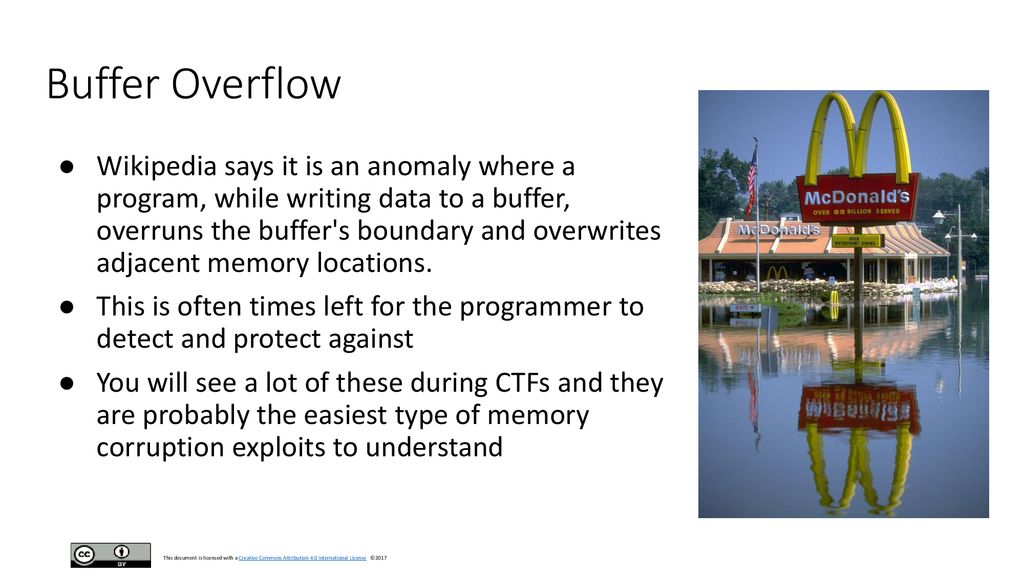
CTF Class 2018 By: Shawn Stone - ppt download

ETCSS: Into the Mind of a Hacker
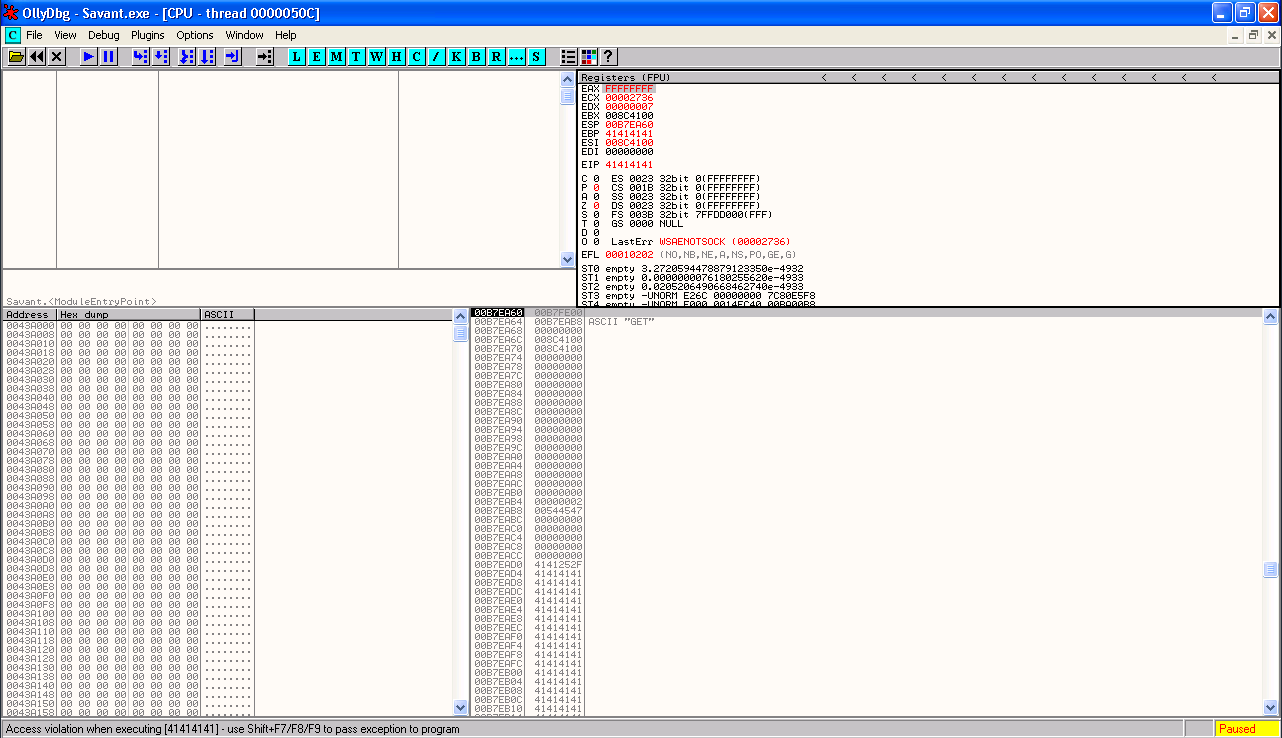
Windows Buffer Overflow Tutorial: An Egghunter and a Conditional Jump · The Grey Corner

Common defect list by Daniel Liezrowice - Issuu
Buffer Overflow: Introduction :: hg8's Notes — My notes about infosec world. Pentest/Bug Bounty/CTF Writeups.
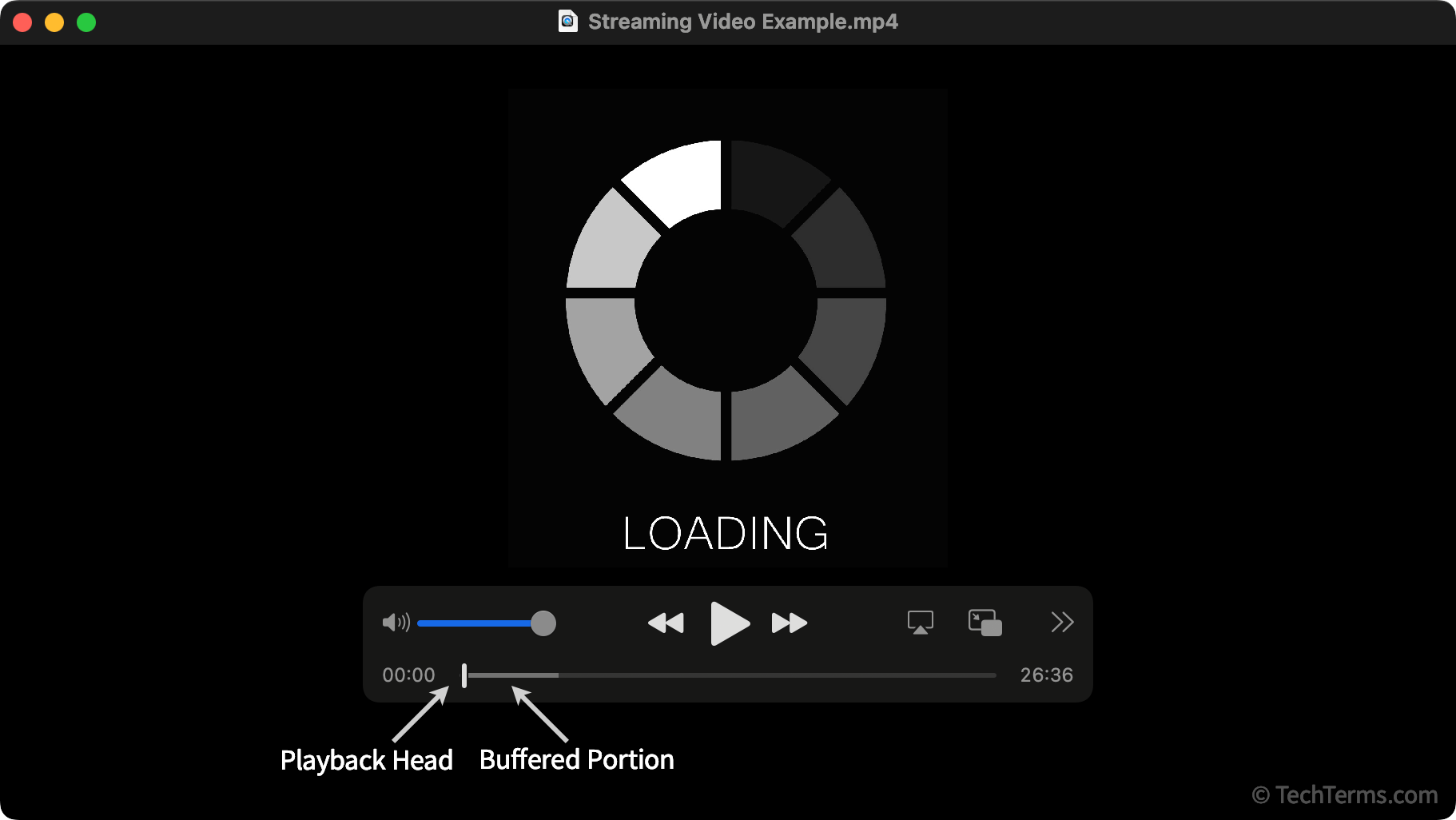
What is Buffer Overflow? — TryHackMe: Buffer Overflow Prep Walkthrough, by caesar

Pointer (computing): Programming Language, Data Type, High-Level Programming Language, Assembly Language, Machine Code, Processor Register, Address Constant, Bounded Pointer, Buffer Overflow : Surhone, Lambert M., Timpledon, Miriam T., Marseken, Susan
Some buffer overrun attacks put the code they want to be executed on the call stack. How can the ability to distinguish between programs and data help to construct a defence against

Understanding & Exploiting stack based Buffer Overflows, by Sourov Ghosh

What is stack based buffer overflow?
What is Buffer Overflow? — TryHackMe: Buffer Overflow Prep Walkthrough, by caesar